Generate Key.json For User Gcloud Cli
Terraform Cloud has three workflows for managing Terraform runs.
Jan 30, 2020 setup-gcloud. This action configures the Google Cloud SDK in the environment for use in actions. The Google Cloud SDK includes both the gcloud and gsutil binaries. It does the following: Downloads a version of the Google Cloud SDK according to the specified version input, as well as the environment OS and architecture. Installs and caches the downloaded version. »The CLI-driven Run Workflow Terraform Cloud has three workflows for managing Terraform runs. The UI/VCS-driven run workflow, which is the primary mode of operation.; The API-driven run workflow, which is more flexible but requires you to create some tooling.; The CLI-driven run workflow described below, which uses Terraform's standard CLI tools to execute runs in. Gcloud auth list # to authenticate with a user identity (via web flow) which then authorizes gcloud and other SDK tools to access Google Cloud Platform. Gcloud auth login # Service Account: to authenticate with a user identity (via a web flow) but using the credentials as a proxy for a service account. Gcloud auth application-default login.
- The UI/VCS-driven run workflow, which is the primary mode of operation.
- The API-driven run workflow, which is more flexible but requires you to create some tooling.
- The CLI-driven run workflow described below, which uses Terraform's standard CLI tools to execute runs in Terraform Cloud.
I created a new GCP account and tried to create a fresh new instance but I cannot ssh into it. Learn more about possible causes of this issue. When I ssh from browser and I can't ssh from CLI. But if I go to my old account, I can ssh into the vm instance on that one just fine. Can you try to ssh on gcloud with verbosity: gcloud compute.
» Summary
The Terraform remote backend brings Terraform Cloud's collaboration features into the familiar Terraform CLI workflow. It offers the best of both worlds to developers who are already comfortable with using Terraform, and can work with existing CI/CD pipelines.
Users can start runs with the standard terraform plan and terraform apply commands, and can watch the progress of the run without leaving their terminal. These runs execute remotely in Terraform Cloud; they use variables from the appropriate workspace, enforce any applicable Sentinel policies, and can access Terraform Cloud's private module registry and remote state inputs.
Terraform Cloud offers two kinds of CLI-driven runs, to support different stages of your workflow:
terraform planstarts a speculative plan in a Terraform Cloud workspace, using configuration files from a local directory. Developers can quickly check the results of edits (including compliance with Sentinel policies) without needing to copy sensitive variables to their local machine.
Speculative plans work with all workspaces, and can co-exist with the VCS-driven workflow.
terraform applystarts a normal plan and apply in a Terraform Cloud workspace, using configuration files from a local directory.
Remote terraform apply is for workspaces without a linked VCS repository. It replaces the VCS-driven workflow with a more traditional CLI workflow.
To supplement these remote operations, you can also use the optional Terraform Enterprise Provider, which interacts with the resources supported by Terraform Cloud. It can be useful for editing variables and workspace settings through the Terraform CLI.
» Remote Backend Configuration
To configure the remote backend, a stanza needs to be added to the Terraform configuration. It must specify the remote backend, the name of a Terraform Cloud organization, and the workspace(s) to use. The example below uses one workspace; see the remote backend documentation for more details.
Next, run terraform login to authenticate with Terraform Cloud. Alternatively, you can manually configure credentials in the CLI config file.
The backend can be initialized with terraform init.
» Implicit Workspace Creation
If you configure the remote backend to use a workspace that doesn't yet exist in your organization, Terraform Cloud will create a new workspace with that name when you run terraform init. The output of terraform init will inform you when this happens.
Generate Key.json For User Gcloud Clinton
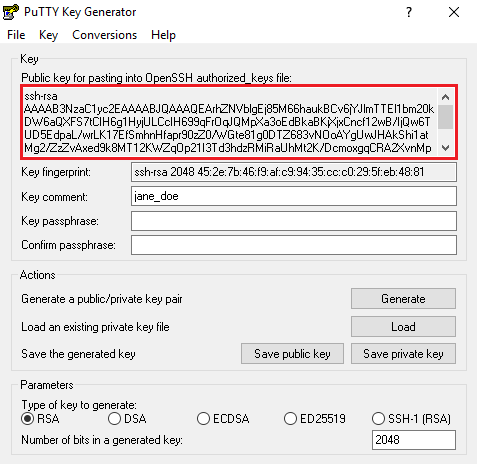
Automatically created workspaces might not be immediately ready to use, so use Terraform Cloud's UI to check a workspace's settings and data before performing any runs. In particular, note that: Generate public key from private key putty.
- No Terraform variables or environment variables are created by default. Terraform Cloud will use
*.auto.tfvarsfiles if they are present, but you will usually still need to set some workspace-specific variables. - The execution mode defaults to 'Remote,' so that runs occur within Terraform Cloud's infrastructure instead of on your workstation.
- New workspaces are not automatically connected to a VCS repository, and do not have a working directory specified.
- A new workspace's Terraform version defaults to the most recent release of Terraform at the time the workspace was created.
» Variables in CLI-Driven Runs
Remote runs in Terraform Cloud use variables from two sources:
- Terraform variables and environment variables set in the workspace. These can be edited via the UI, the API, or the
tfeTerraform provider. - Terraform variables from any
*.auto.tfvarsfiles included in the configuration. Workspace variables, if present, override these.
Note: Remote runs do not use environment variables from your shell environment, and do not support specifying variables (or .tfvars files) as command line arguments.
» Remote Working Directories
If you manage your Terraform configurations in self-contained repositories, the remote working directory always has the same content as the local working directory.
If you use a combined repository and specify a working directory on workspaces, you can run Terraform from either the real working directory or from the root of the combined configuration directory. In both cases, Terraform will upload the entire combined configuration directory.
» Excluding Files from Upload
Version note:.terraformignore support was added in Terraform 0.12.11.
CLI-driven runs upload an archive of your configuration directoryto Terraform Cloud. If the directory contains files you want to exclude from upload,you can do so by defining a .terraformignore file in your configuration directory.
» Remote Speculative Plans
To run a speculative plan on your configuration, use the terraform plan command. The plan will run in Terraform Cloud, and the logs will stream back to the command line along with a URL to view the plan in the Terraform Cloud UI.
Users can run speculative plans in any workspace where they have plan access.
Speculative plans use the configuration code from the local working directory, but will use variable values from the specified workspace.
» Remote Applies
When configuration changes are ready to be applied, use the terraform apply command. The apply will start in Terraform Cloud, and the command line will prompt for approval before applying the changes.
Remote applies require write access to the workspace.
Remote applies use the configuration code from the local working directory, but will use variable values from the specified workspace.
Important: You cannot run remote applies in workspaces that are linked to a VCS repository, since the repository serves as the workspace’s source of truth. To apply changes in a VCS-linked workspace, merge your changes to the designated branch.
» Sentinel Policies
If the specified workspace uses Sentinel policies, those policies will run against all speculative plans and remote applies in that workspace. The policy output will be available in the terminal. Hard mandatory checks cannot be overridden and they prevent terraform apply from applying changes.
References
Other cheatsheets
multiple gcloud config
auth
kubectl uses OAuth token generated by
gcloud config config-helper --format jsongcloud config config-helper --format='value(credential.access_token)'gcloud auth print-access-tokengenerates new token
info
zones
To return a list of zones given a region
projects
billing
Generate Key.json For User Gcloud Cli File
switch gcloud context with gcloud config
service account and IAM
List IAM policy on the project level
service account level
GCS bucket level
app engine
cloud build
Cloud build trigger GCE rolling replace/start
kms
gcloud command for creating an instance?
from web console
instances, template, target-pool and instance group
MIG with startup and shutdown scripts
route
tag the instances with no-ips
firewall rules
layer 3 network lb
Generate Key.json For User Gcloud Cli Mac
layer 7 http lb
forwarding-rules
address
compute engine image
list an instance
move instance
gcloud compute instances move <instance_wanna_move> --destination-zone=us-central1-a --zone=us-central1-c
ssh & scp
ssh port forwarding for elasticsearch
The 2nd localhost is relative to elasticsearch-1`
ssh reverse port forwarding
for example, how to connect to home server's flask server (tcp port 5000) for a demo or a local game server in development